Key Features
Explore Our Features to Keep Your Data Safe
Your Trusted Partner in Data Protection with Cutting-Edge Solutions for
Comprehensive Data Security.
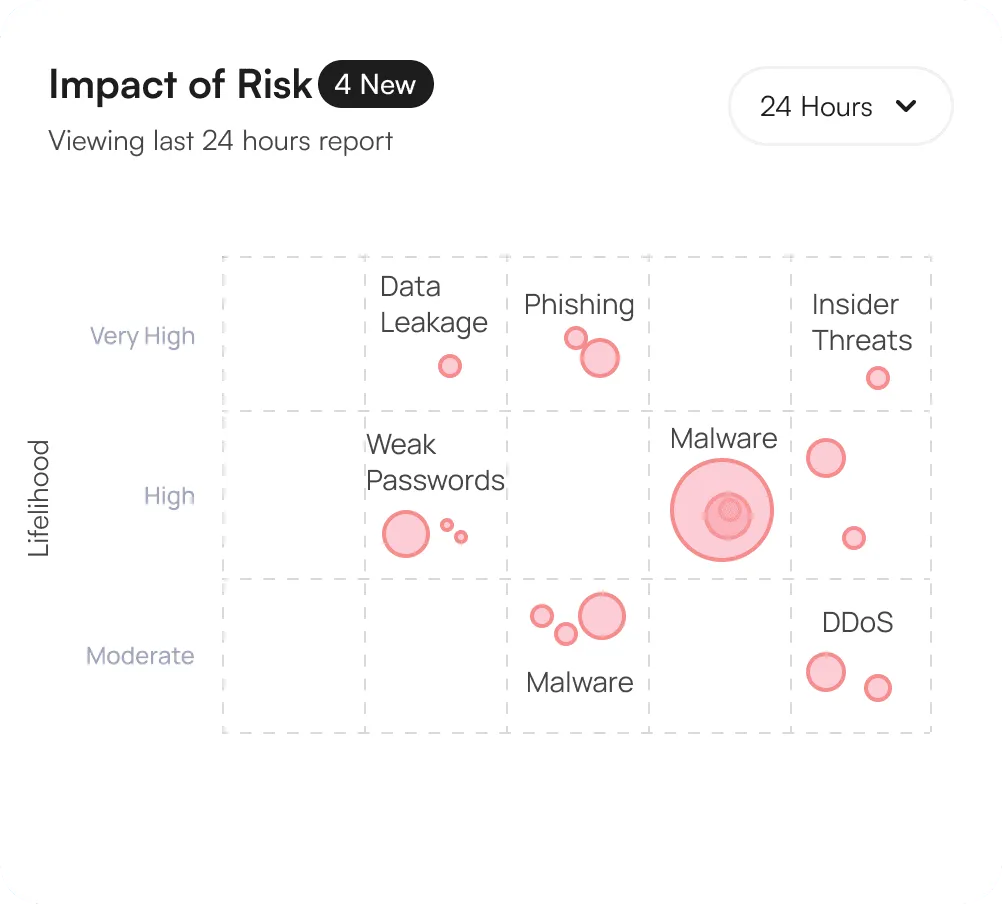
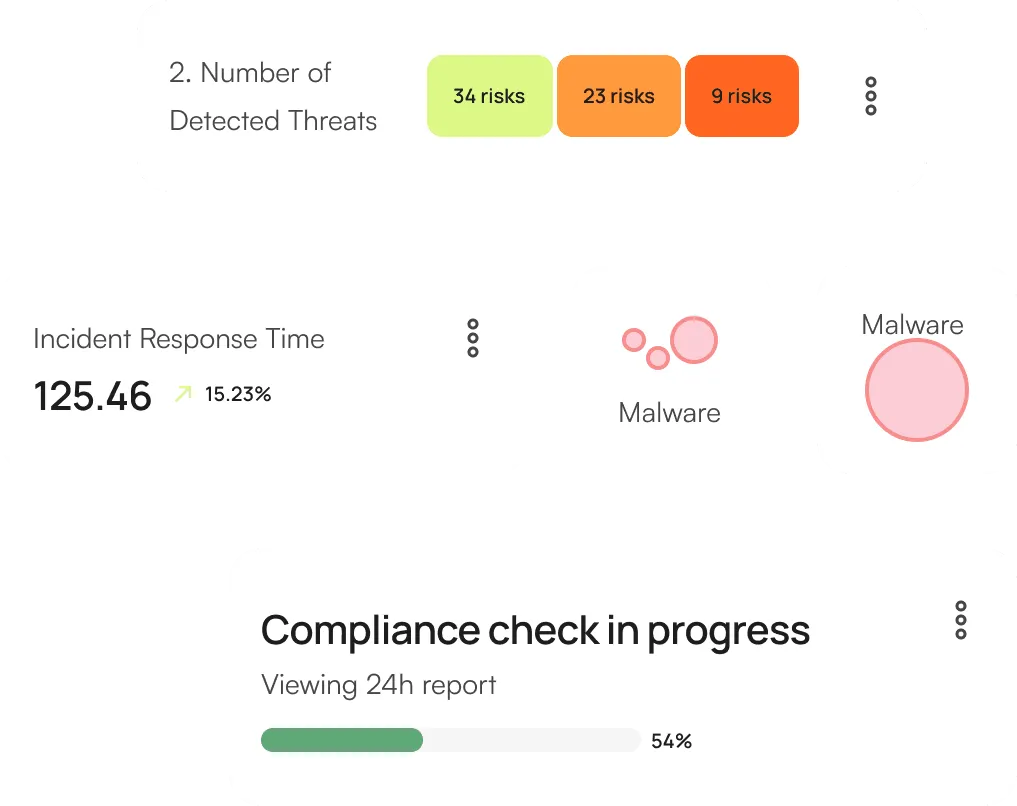
Continuously evaluates potential security threats and impact
This includes suggesting security patches, policy updates, and other preventive measures to reduce the likelihood and impact of threats.
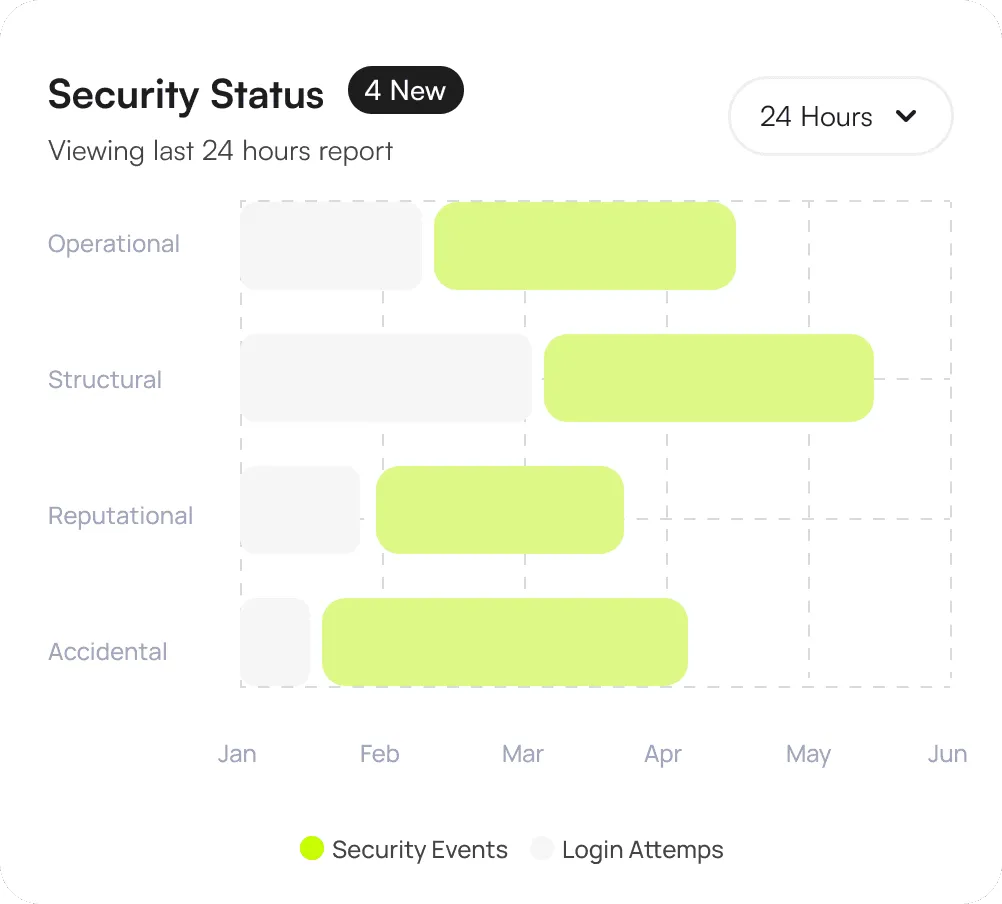
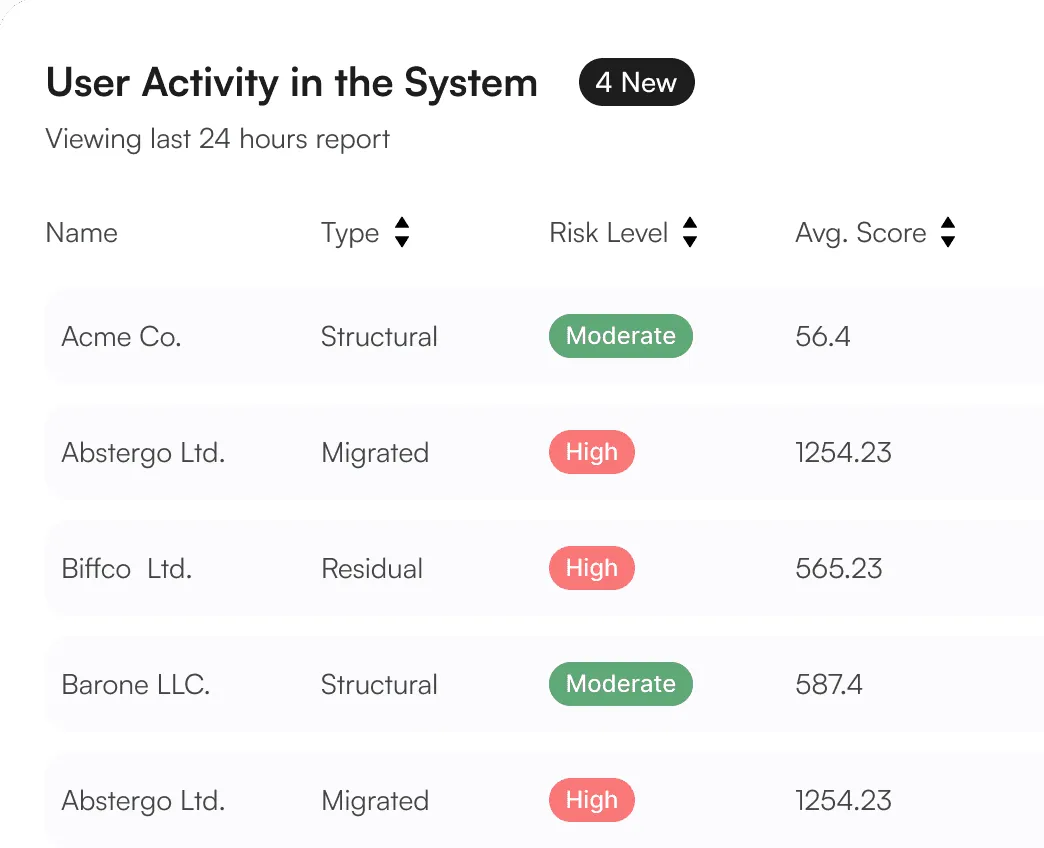
Presents a view of your organization security posture
Allows you to set thresholds for security parameters and receive real-time alerts when these thresholds are breached ensuring you stay informed of critical events.
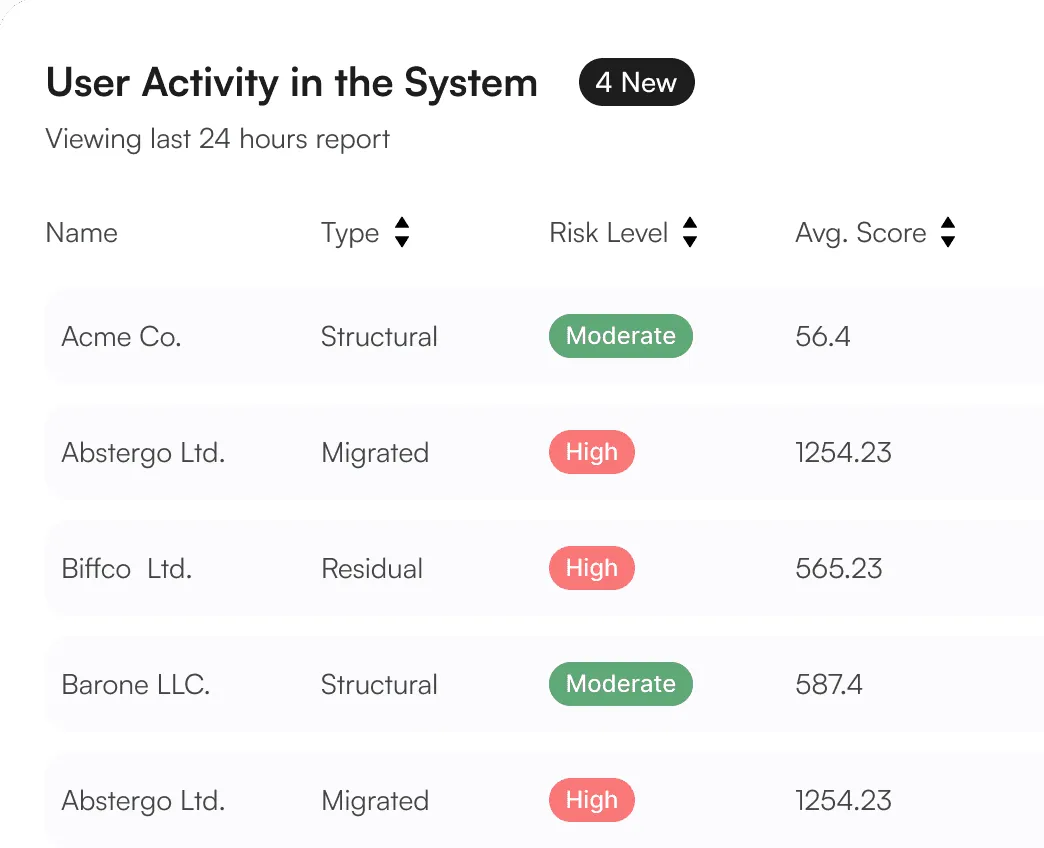
Monitors and logs all the data access events
Monitors and logs all data access events, including who accessed what data, when, and from where. This provides a clear audit trail for compliance and security investigations.
Learn More Details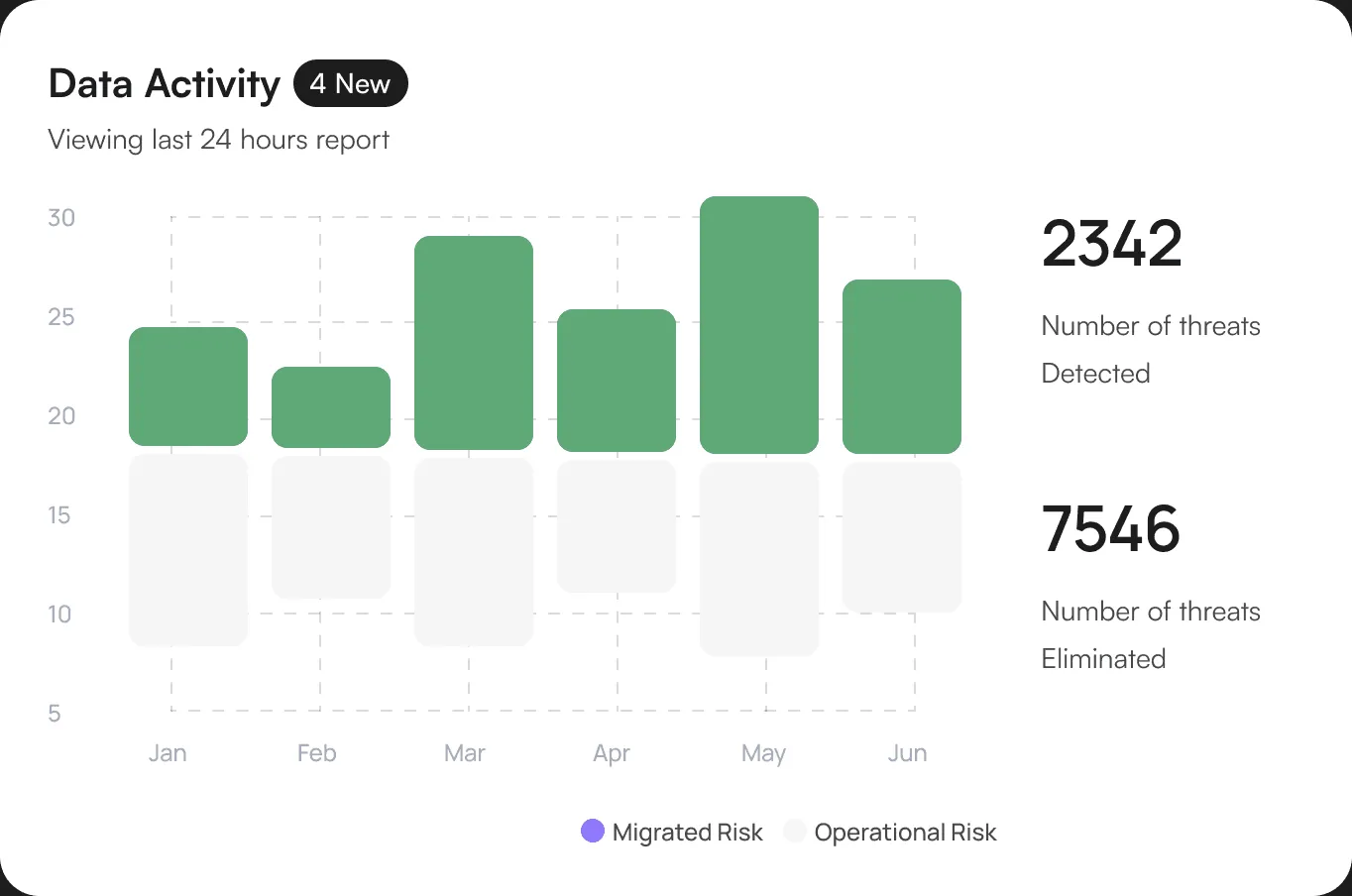
Essential Feature
Discover the Features That Makes SecureTrustCyber Stand Out.
Your Trusted Partner in Data Protection with Cutting-Edge Solutions for
Comprehensive Data Security.
Threat Prevention
Our advanced threat prevention capabilities keep you safe from a wide range of cyber threats.
Firewall-as-a-Service (FWaaS)
Cloud-delivered firewall to protect all your users and devices.
Secure Web Gateway (SWG)
Block threats and control internet access with our secure web gateway.
Intrusion Prevention System (IPS)
Prevent network intrusions with our advanced IPS technology.
Malware Prevention
Stop malware in its tracks before it can infect your systems.
DNS Security (DNS)
Secure your DNS traffic and prevent access to malicious domains.
Remote Browser Isolation (RBI)
Isolate web browsing activity to protect your network from web-based threats.
Data and App Protection
Protect your sensitive data and applications with our comprehensive security solutions.
Cloud Access Security Broker (CASB)
Gain visibility and control over your cloud apps and data.
Data Loss Prevention (DLP)
Prevent sensitive data from leaving your network.
Zero Trust Network Access (ZTNA)
Provide secure access to your applications based on a zero-trust model.
AI Security (AISEC)
Leverage AI to detect and respond to threats in real-time.
Detection and Response
Detect and respond to threats quickly and effectively with our advanced detection and response capabilities.
Extended Detection and Response (XDR)
Unify security data from multiple sources for faster detection and response.
Endpoint Protection (EPP/EDR)
Protect your endpoints with our comprehensive EPP and EDR solution.
Secure Your Data with SecureTrustCyber Protection Solution
Allows you to set thresholds for security parameters and receive real-time alerts when these thresholds are breached.
Get Started